SOC Analyst: Detect. Respond. Protect.
About
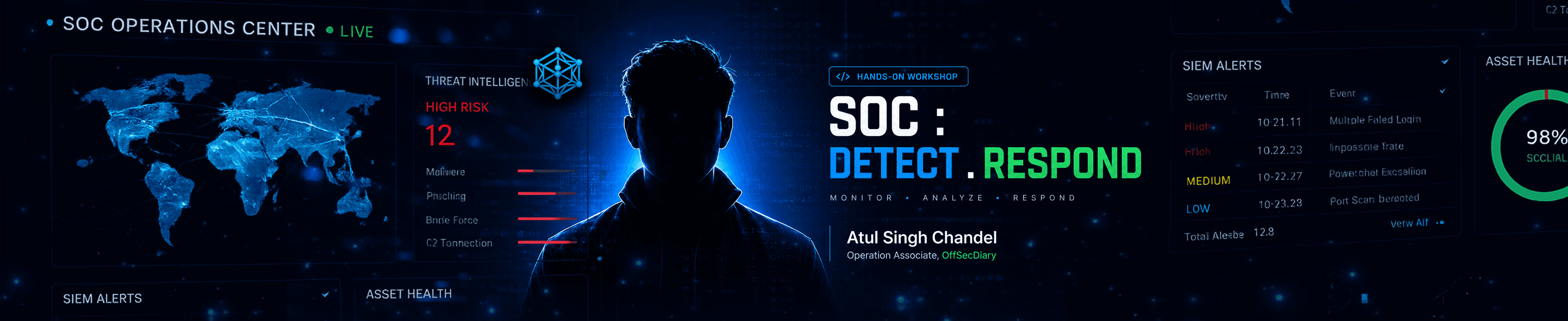
SOC Analyst: Detect. Respond. Protect.
This hands-on workshop introduces participants to the role of a SOC (Security Operations Center) Analyst through practical cybersecurity workflows, attack simulations, and real-time log monitoring. Participants will learn how modern SOC teams detect, analyze, and respond to cyber threats using tools like Kali Linux, Wazuh SIEM, and VirtualBox while understanding real-world incident response processes used in the cybersecurity industry
01
SOC Fundamentals
Understand how Security Operations Centers monitor, detect, investigate, and respond to cyber threats using people, processes, and security technologies.
02
Practical Attack Simulation
Learn how brute-force attacks, phishing attempts, and suspicious activities are simulated and detected using Kali Linux and Wazuh SIEM dashboards.
03
Wazuh SIEM Implementation
Participants will explore practical SIEM setup, log monitoring, alert analysis, and real-time event investigation workflows used in cybersecurity operations.
What you will learn
Understand the role and workflow of a SOC Analyst
Learn how SIEM tools monitor and detect threats
Gain practical exposure to cybersecurity lab setup
Understand attack detection and response workflows
Learn beginner roadmap for SOC and blue-team careers
What's in it for you?
Validation for your skills. Recognition for your hustle.
Official Badge
Digital credentials to showcase your expertise on professional platforms like LinkedIn.
Expert-Led Insights
Curated architectural knowledge delivered directly by domain specialists.
Strategic Edge
Master high-performance design patterns that out-scale legacy approaches.
Community Access
Join a private cohort of peers and get lifetime access to our alumni network.
Meet your speaker
Atul Singh Chandel is a cybersecurity practitioner and blue-team enthusiast focused on SOC operations, threat detection, and practical security monitoring. He works on hands-on cybersecurity implementations involving SIEM tools, attack simulation environments, and incident response workflows, with strong interest in helping learners build real-world defensive security skills.
Event timeline
Registration Starts
Registrations open, with email confirmation, WhatsApp community access, and session details shared after sign-up.
Live Session
During the scheduled session time, the website access changes from Registered to Join Workshop for participants.
